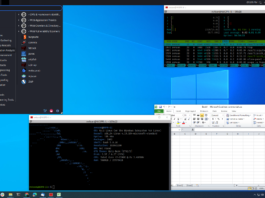
A year-old Webmin backdoor revealed at DEF CON 2019 allowed unauthenticated attackers to execute...
Earlier this month, at DEF CON 2019, a Turkish security researcher, Özkan Mustafa Akkuş presented a zero-day remote code execution vulnerability in Webmin, a...
Moscow’s blockchain-based internet voting system uses an encryption scheme that can be easily broken
Russia is looking forward to its September 2019 elections for the representatives at the Parliament of the city (the Moscow City Douma). For the...
Cisco Talos researchers disclose eight vulnerabilities in Google’s Nest Cam IQ indoor camera
On Monday, August 19, the Cisco Talos research team disclosed eight security vulnerabilities in Google’s Nest Cam IQ, a high-end security indoor camera (IoT...
A security issue in the net/http library of the Go language affects all versions...
On August 19, the Kubernetes Community disclosed that a security issue has been found in the net/http library of the Go language affecting all...
Security researcher publicly releases second Steam zero-day after being banned from Valve’s bug bounty...
Updated with Valve’s response: Valve, in a statement on August 22, said that its HackerOne bug bounty program, should not have turned away Kravets...
GitHub now supports two-factor authentication with security keys using the WebAuthn API
Yesterday, GitHub announced that it now supports Web Authentication (WebAuthn) for security keys. In addition to time-based one-time password (TOTP) applications and text messages,...
New Bluetooth vulnerability, KNOB attack can manipulate the data transferred between two paired devices
Recently, a group of researchers exposed a severe vulnerability called Key Negotiation Of Bluetooth (KNOB) that allows an attacker to break the Bluetooth Basic...
Security flaws in Boeing 787 CIS/MS code can be misused by hackers, security researcher...
At the Black Hat 2019 security conference in Las Vegas, Ruben Santamarta, an IOActive Principal Security Consultant in his presentation said that there were...
iPhone can be hacked via a legit-looking malicious lightning USB cable worth $200, DefCon...
While our phones are running low on battery, we do not think twice before inserting a USB to charge it. Also, while transferring files...
Amazon EBS snapshots exposed publicly leaking sensitive data in hundreds of thousands, security analyst...
Last week the DefCon security conference, which was held in Paris and Las Vegas, revealed that companies, govt and startups are inadvertently leaking their...










![How to create sales analysis app in Qlik Sense using DAR method [Tutorial] Financial and Technical Data Analysis Graph Showing Search Findings](https://hub.packtpub.com/wp-content/uploads/2018/08/iStock-877278574-218x150.jpg)