Building an app using Backbone.js
(For more resources related to this topic, see here.)
Building a Hello World app
For building the app you will need the necessary script files and...
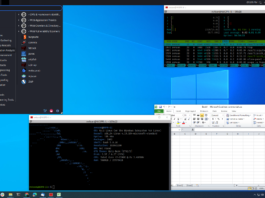
Kali Linux Social Engineering Toolkit Tutorial: Credential Harvester
An example of a social engineering attack using Kali Linux - use a credential harvester to gather the victim's credentials. Redirect your victim to...
Planning the lab environment
(For more resources related to this topic, see here.)
Getting ready
To get the best result after setting up your lab, you should plan it properly...
Getting Started with Spring Security
(For more resources related to this topic, see here.)
Hello Spring Security
Although Spring Security can be extremely difficult to configure, the creators of the product...
Wireshark: Working with Packet Streams
(For more resources related to this topic, see here.)
Working with Packet Streams
While working on network capture, there can be multiple instances of network activities...
BackTrack Forensics
(For more resources related to this topic, see here.)
Intrusion detection and log analysis
Intrusion detection is a method used to monitor malicious activity on a...
The DPM Feature Set
Microsoft Data Protection Manager 2010
A practical step-by-step guide to planning deployment, installation, configuration, and troubleshooting of Data Protection Manager 2010 with this book and...
Installing Data Protection Manager 2010
With the DPM upgrade you will face some of the same issues as with the installation such as what are the prerequisites? is your...
Overview of Data Protection Manager 2010
Microsoft Data Protection Manager 2010
A practical step-by-step guide to planning deployment, installation, configuration, and troubleshooting of Data Protection Manager 2010
Read more about this book
(For...
FAQs on BackTrack 4
BackTrack 4: Assuring Security by Penetration Testing
Master the art of penetration testing with BackTrack
Q: Which version of Backtrack is to be...










![How to create sales analysis app in Qlik Sense using DAR method [Tutorial] Financial and Technical Data Analysis Graph Showing Search Findings](https://hub.packtpub.com/wp-content/uploads/2018/08/iStock-877278574-218x150.jpg)