Last month, researchers from USA, China, and Hong Kong published a paper in collaboration, titled as ‘Beware of Your Screen: Anonymous Fingerprinting of Device Screens for Off-line Protection’. This paper, presented at The 34th Annual Computer Security Applications Conference, highlights a new technique to enhance the security protection of QR-based payment, without undermining the payer’s privacy.
The technique used by the researchers takes advantage of the unique luminance unevenness of a payer’s screen that is introduced by the imperfect manufacture process. The paper also presents a way to ensure that even when the payer’s digital wallet has compromised, an unauthorized payment cannot succeed. Besides this, the paper also takes into consideration the privacy issues that may arise if the screen’s features were naively deployed to authenticate the payer; as it could be misused by the vendors to link one’s different purchases together. To tackle this, the researchers have presented ‘AnonPrint’ that obfuscates the phone screen during each payment transaction.
QR-code mobile payment systems are used by almost everyone today, including banks, service providers, and other commercial organizations. These payment systems are deployed solely using software without any hardware support. The paper highlights that in the absence of hardware support, a users wallet ‘can be vulnerable to an Os-level adversary’ which could be misused to generate a user’s payment tokens.
To overcome this adversary, the researchers have demonstrated a method as a second factor authentication mechanism in the form of the physical features of a mobile’s screen. The research takes advantage of the taried luminance levels of the pixels on the screen (which occurs due to the flaws in the manufacturing process) and can be used to uniquely characterize the screen. An advantage of this method is that, since the adversary cannot observe the physical features of the screen the physical fingerprint cannot be stolen even when the OS is fully compromised. Also, this second-factor authentication is fool-proof even when the secret key for generating QR codes is stolen or when a user’s phone has been fully compromised by the adversary.
How is Anonymous screen Fingerprinting carried out?
In order to enable service providers to utilize the screen to enhance security protection as well as preserve users privacy, the researchers have designed a new technique called ‘AnonPrint’. AnonPrint randomly generates visual one- time masks which is a pixel pattern with dots set to various brightness levels to obfuscate the distinguishable features of a user’s screen.
The technique randomly creates a smooth textured pattern for each transaction (this pattern is also known to the provider), and displays a pattern as the background of QR code to disarrange the brightness of a screen, in line with the screen’s real-world physical properties i.e. the neighboring dots are correlated and the levels of brightness change smoothly.
This will hide the physical properties of a screen, and the party that knows the mask, like the payment service provider, can verify whether the features collected from the protected screen are related to the authorized device or not.
Here is an overview of how the system works:
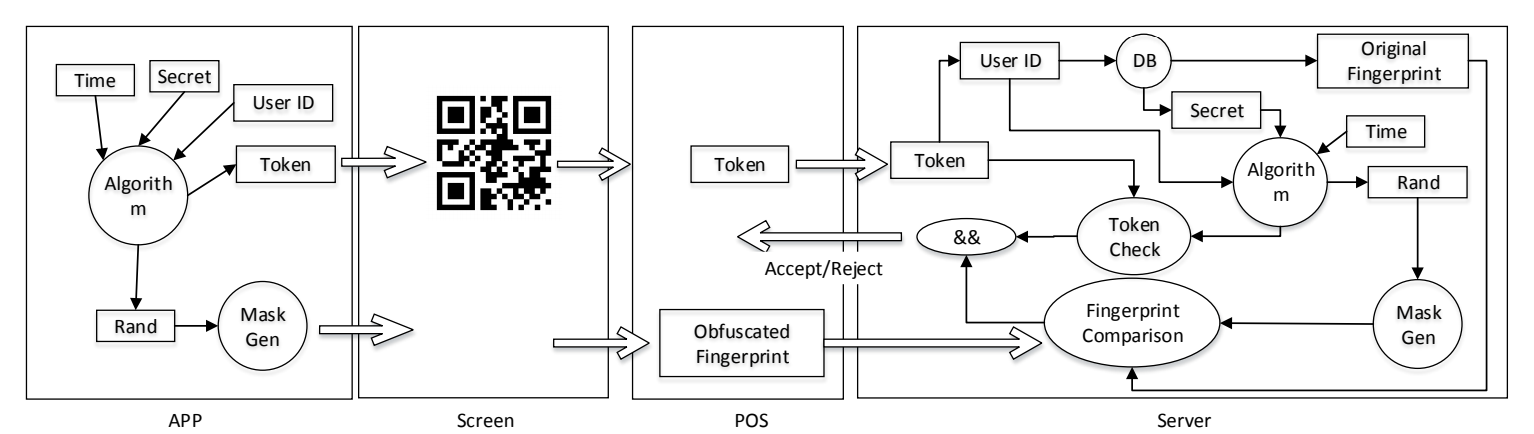
- First, the user needs to submit the original screen fingerprint of their device to the payment provider when they open an account.
- The wallet app is modified to synchronize a secret random seed with the provider. This seed could be achieved through hashing the time for the payment together with a shared secret using a cryptographic hash function (e.g., SHA-256). This duo then bootstraps a pseudo random number generator (PRNG) each time when the wallet app needs to provide each party a sequence of random numbers for mask generation. The mask is displayed as the background for displaying the QR payment token, from which the POS scanner extracts the obfuscated screen fingerprint in addition to decoding the QR code, finally passing the information to the payment provider.
- The provider retrieves the shared secret and the original screen fingerprint using the claimed ID. Next, the same mask used by the payer is re-constructed and used with the with the original ngerprint as inputs for synthesizing a new obfuscated fingerprint. This is compared with the fingerprint from the payer’s screen and the transaction can be approved the similarity of these two prints is above a certain threshold and other security checks are completed.
How does AnonPrint obfuscate the screen?
AnonPrint creates a ‘mask’, to hide the screen’s hardware fingerprint for every payment transaction. Such a mask is automatically generated by a digital wallet app, seeding a PRNG with a random number synchronized with the payment service provider.
To obfuscate this hardware fingerprint and to maintain a screen’s realistic look, the researchers performed the following steps:
(1) They first performed a ‘Random zone selection’, in which they produced a 180*108 pure white (with all pixels set to 255) image as the background and randomly selected from the image 20 mutually disjoint zones, each of size 16*16.
(2) Next, came the ‘Dot darkening’ step. From each zone, they randomly chose 3 pixels and set their pixel value to a random number between 0 to 100.
(3) The team then performed Smoothing in which for every zone, AnonPrint blurs it using Gaussian Smoothing that , “smoothes out” the dark color of the selected pixels to its neighboring pixels.
(4) Finally, they performed ‘Resizing’ where the mask image is resized and scaled to a 1800*1080 matrix whose values range from 220 to 255. The size of this image is iden-
tical to the original fingerprint.
Each user needs to register to the payment provider with an image of their unprotected screen when all pixels are set to the maximum gray-scale. During the payment, an image of a masked screen is used to authenticate the payer done on the payment service provider’s side by reconstructing the mask using the shared secret, and then obfuscate the fingerprint for comparing with the image from the vendor.
Results and Discussion
The researchers conducted various experiments in which they collected 100 smartphones- including iPhone, Samsung and many others. All 100 phones were used to understand the effectiveness of the screen fingerprint in identifying the device. 50 phones were used to evaluate the anonymity protection and the effectiveness of AnonPrint separately. iPhone 6s was used to capture images for screen fingerprinting.
They implemented an Android application to display QR code and obfuscate a screen using masks derived from given random numbers for anonymous payment. To collect the fingerprints from each device, they displayed a QR code without obfuscation, and then continue to show 5 different masks on the screen with the same code. Each time, they took a picture from the screen and used the image to extract fingerprints.
Their experiment concluded that for 88.75% of transactions, the vendors can accurately identify other transactions from the same customer, by simply looking at the features of their screens. Their experiment also proved that Anon Print indeed breaks vendors’ capability of linking screen fingerprint and that the overhead introduced by AnonPrint (only 50ms) is small for the offline payment. Fingerprint verification takes 2.4 seconds on average to be completed. You can head over to the paper for a detailed explanation on every experiment conducted to check fingerprint accuracy, anonymity protection, fingerprint verification and much more.
The research results look promising and it will be interesting to see some potential implementation in the QR-payment systems of today.
Head over to the paper for more insights on this news.
Read Next










![How to create sales analysis app in Qlik Sense using DAR method [Tutorial] Financial and Technical Data Analysis Graph Showing Search Findings](https://hub.packtpub.com/wp-content/uploads/2018/08/iStock-877278574-218x150.jpg)


